Key Summary
- Regulatory Status: Under 2026 guidance, tokens are Digital Securities. Compliance is based on “economic reality,” requiring strict adherence to federal laws for distribution, KYC/AML, and reporting.
- Programmable Compliance: Tokenization allows transfer restrictions and eligibility gating to be baked into the asset layer. Success requires an automated, “audit-ready” model rather than a one-time checkbox.
- Institutional Custody: Custody must be a comprehensive control system—not just a wallet—featuring clear legal rights, multi-layer approval workflows, and robust recovery protocols.
Security Tokens as Institutional-Grade Operations
No longer a distant vision, security tokens are now the standard for institutional-grade regulated operations. Wall Street is already running real money through token rails, such as BNY Mellon plugging LiquidityDirect into Goldman Sachs’s Digital Asset Platform (GS DAP) via the Canton Network. This allows institutions to redeem tokenized money-market fund positions with near-instant settlement finality.
To launch a program that institutions, auditors, and risk teams will approve, you need more than token issuance. You need a working stack for compliance, custody, monitoring, and reporting. Most programs fail due to weak operating design: unclear legal structures, incomplete transfer controls, and poor custody governance.
What is A Security Token?
A security token is a digital representation of a regulated financial instrument—such as equity, debt, or fund interests—issued and transferred using digital rails. The SEC’s January 2026 Joint Statement reinforces that tokenization is a technological method of recordkeeping, not a legal innovation that alters the underlying regulatory status.
In practice, the key executive question is not “Is it on-chain?” but: What rights does it represent, how is it distributed, and what controls govern ownership and reporting? Following the March 2026 SEC-CFTC MOU, U.S. regulators now utilize a unified taxonomy where these assets are typically classified as “Digital Securities.”
Why Do Executives Care Now?
Security tokens deserve attention now because they provide clear operational benefits for regulated capital markets:
- Shorter Operational Cycles: Automated workflows end-to-end instead of manual steps.
- Programmable Compliance: Transfer restrictions and eligibility gating are enforced at the token and wallet layer.
- Institutional Legitimacy: The Eurosystem’s January 2026 decision to accept DLT-based assets as eligible collateral proves tokenized securities are now a core component of global liquidity.
The Compliance Reality: Tokenized Securities Still Follow Securities Rules
Tokenization changes the plumbing of finance, not the law. Regulators are clear: if it functions like a security, it is regulated as one. Compliance isn’t a pre-launch checkbox—it’s the foundational operating model that determines if your asset can survive institutional diligence.
For executives, the takeaway is simple: A whitepaper is not a compliance strategy. True compliance requires an integrated stack where issuance, transfer rules, and custody map directly to existing securities obligations—providing audit-ready evidence that your controls hold up under stress.
1. Classification comes first
Under the Atkins-led SEC, the 2026 interpretive guidance has clarified that “substance governs treatment.”
- US: The SEC and CFTC now coordinate via a formal federal policy framework, focusing on “economic reality” rather than labels.
- EU: If an asset is a financial instrument under MiFID II, it must follow the DLT Pilot Regime (for trading/settlement) or MiCA (for other crypto-assets). Note: The MiCA “grandfathering” period ends July 1, 2026, making full authorization mandatory for European operators.
2. Offering structure determines your obligations
Capital formation for security tokens usually maps to familiar pathways, just with different plumbing:
- Private placements (institutional / accredited-style distribution)
- Offshore distributions with jurisdiction and solicitation discipline
- Public offers only when your disclosure and licensing posture supports it
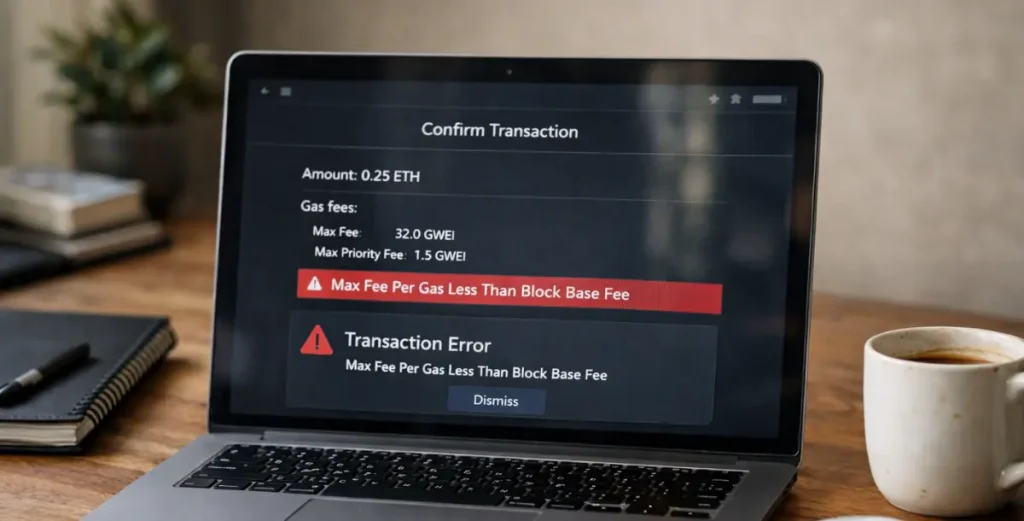
Where teams blow up: they design a token launch like a product launch, then discover the distribution path dictates everything including eligibility, Know-Your-Customer (KYC) depth, transfer restrictions, secondary venues, marketing claims.
3. Secondary trading is not optional and not “free”
If buyers can resell, you need a defensible market-structure path: broker-dealer / Alternative Trading System (ATS) / exchange equivalents, surveillance expectations, and transfer controls that match who can trade and when. EU supervisors explicitly treat market integrity and operational controls as core requirements, not nice-to-haves, once activity scales.
Why Your Custody Model Will Make or Break Your Regulatory Approval
Security token projects often stall for a boring reason: nobody can sign off on custody and control. The issue is rarely the token itself, but whether your custody setup can survive legal, compliance, and risk review.
Executives should treat custody as a control system, not a wallet feature. A diligence-ready custody design must answer the following questions clearly:
- Legal Holding Model: Who holds the asset, in what name, and with what segregation?
- Control Model: Who can move assets, under what approvals, limits, and allowlists?
- Evidence Model: What can auditors and risk teams verify repeatedly without manual workarounds?
- Failure Model: What happens during outages, compromises, insolvency events, or key-loss scenarios?
This is exactly why institutions and standard-setting bodies keep pushing stronger custody posture in tokenization programs. Tokenization can introduce new ambiguity around ownership, control, and operational responsibility if the custody layer is not engineered properly.
The Operating Stack Security Tokens Require
A compliant security-token programme looks less like issuing a token and more like assembling a regulated operating stack:
- Issuer + legal wrapper (the entity and instrument terms)
- Distribution controls (eligibility, KYC/AML, jurisdiction gating, marketing discipline)
- Tokenization + lifecycle logic (issuance, transfers, lockups, corporate actions)
- Custody-grade wallet controls (permissions, approvals, segregation, recovery)
- Monitoring + case management (risk flags, sanctions exposure, escalation trails)
- Reconciliation + reporting (position proof, transaction trails, audit packs)
When teams skip these layers, they get reconciliation debt and instruments that counterparties will not support.
This is where advisory and implementation support matters. Launching compliant security tokens is a programme design challenge across legal, compliance, operations, treasury, and custody. Teams need a practical rollout plan for how the stack works in production, not just a token minted on-chain.
Security Tokens Win When You Productize Compliance and Custody
Security tokens succeed because you remove friction without removing safeguards. If you’re building or scaling a programme, ChainUp provides the infrastructure layer that makes it operable: a complete institutional-grade environment that unifies secure asset management, automated governance, and audit-ready reporting. Connect with us to activate your DeFi roadmap and explore the possibilities.